It seems like not a day goes by that one of the businesses which Homeland Secure IT assists here in the Upstate of South Carolina doesn’t reach out with a question about an email they received.
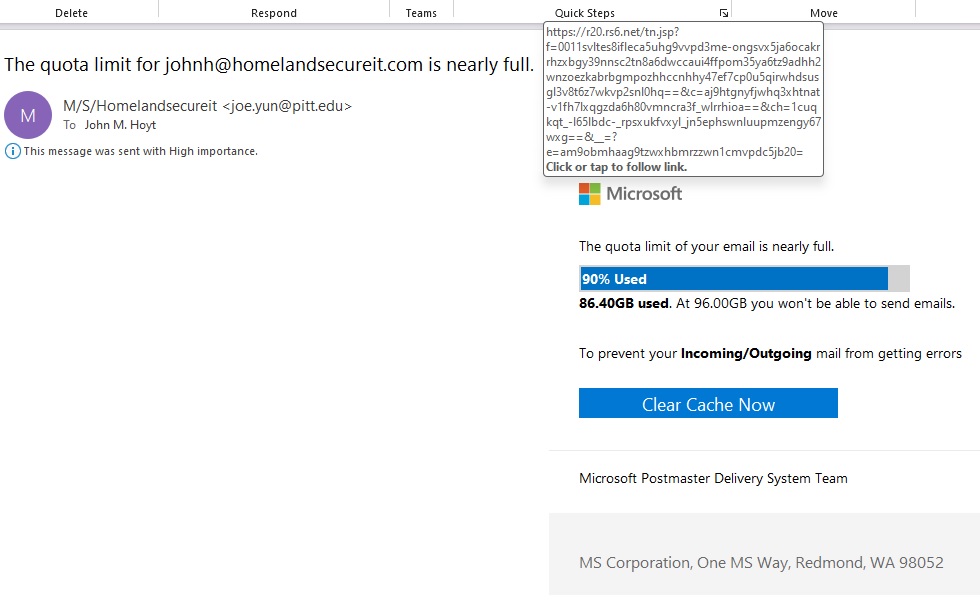
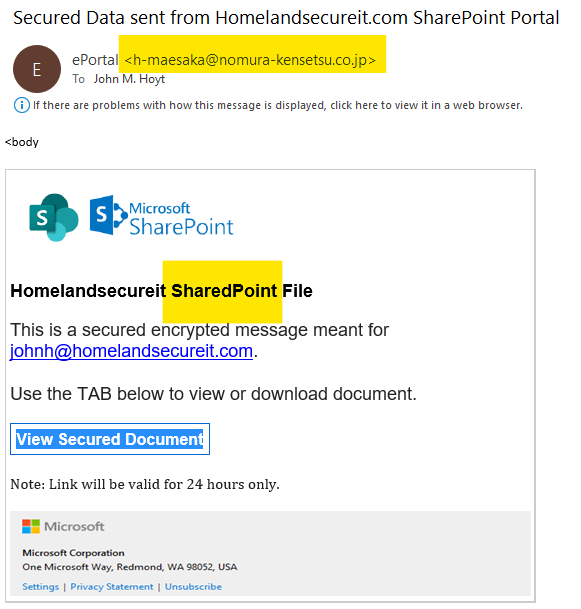
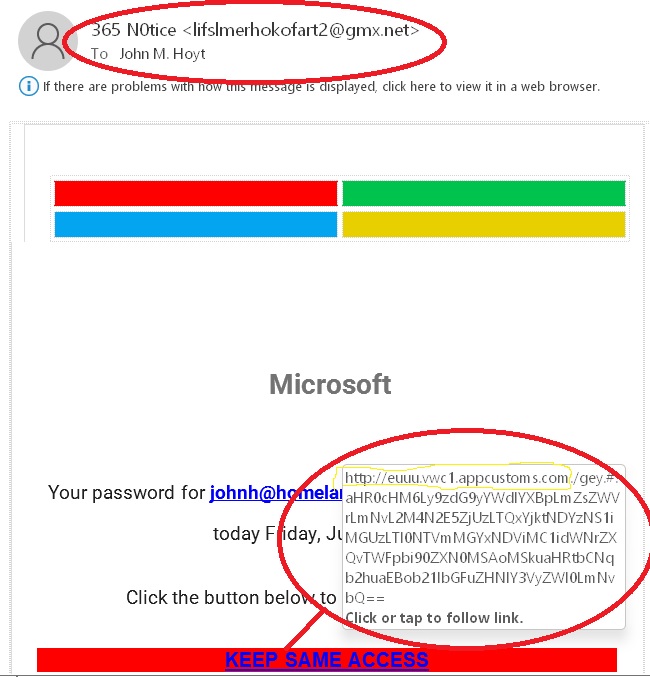
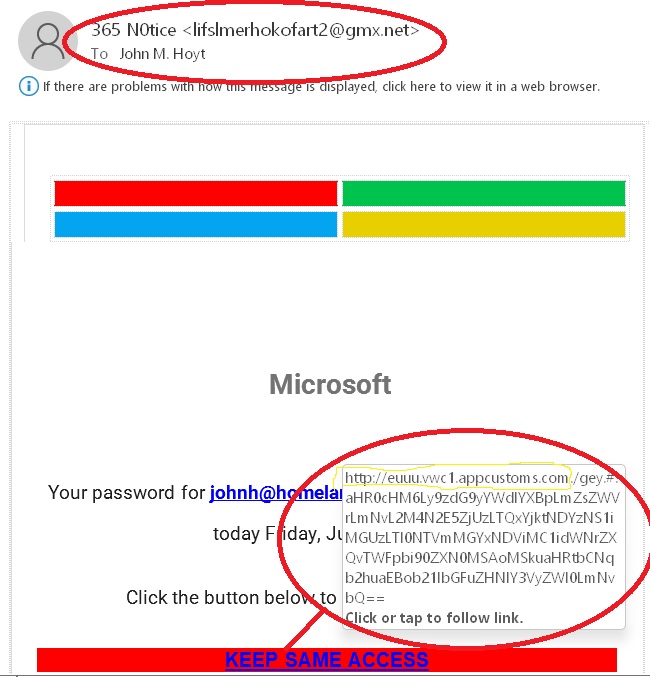
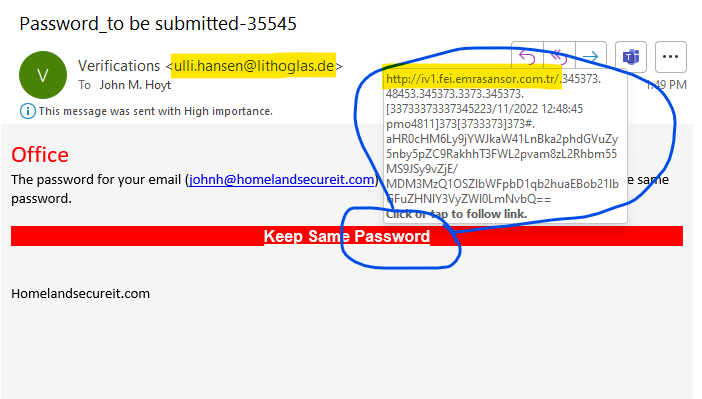
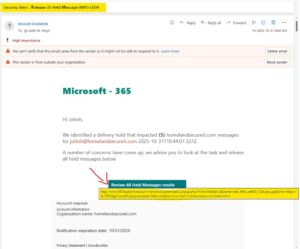
Guess what? We get them too! Today’s poorly crafted attempt has a subject of “Security Alert : Release (5) Held Message (NBY)-LESN”, but if you look at it closely, you will see that there are special characters in the subject used to fool filters.
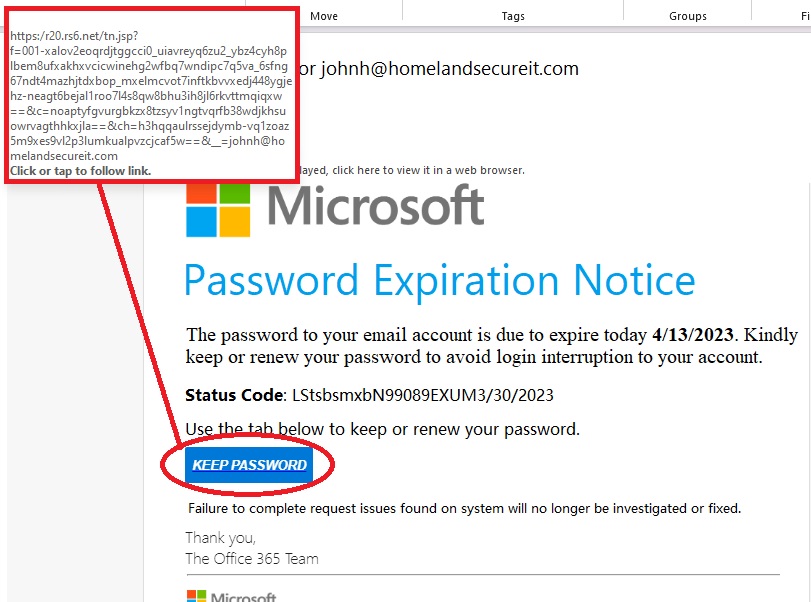
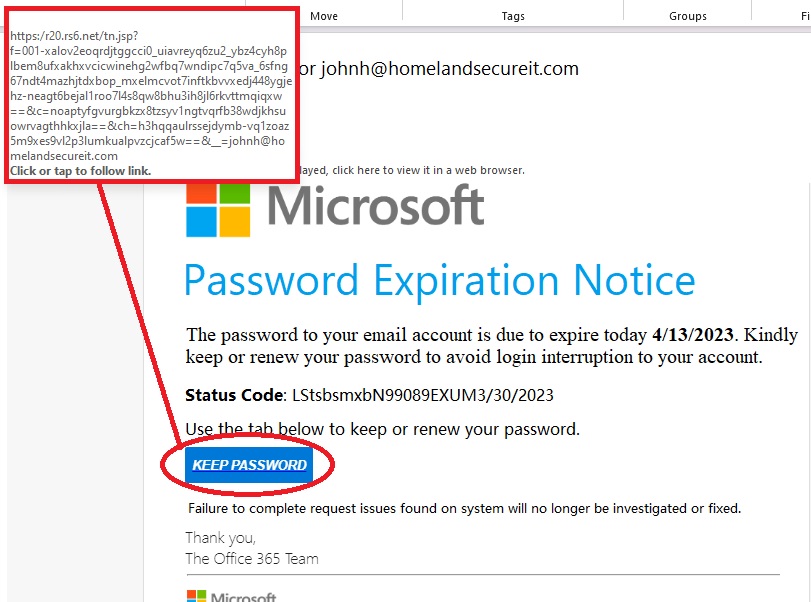
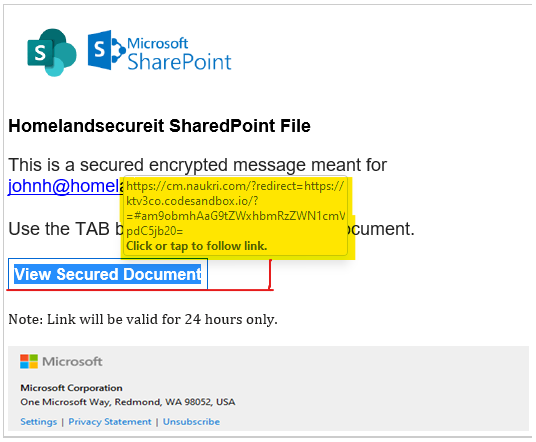
Further examination reveals the true purpose. If you hover over the “Review All Held Message results” button, it exposes the URL, which has no association to Microsoft what-so-ever.
Anyone who clicks that link without thinking, would be taken to a site that could look just like a Microsoft site and would perhaps prompt for credentials. Without thinking, the person might be tricked into entering their login information, and the site might automatically pipe that over to an authentic Microsoft site which would send a multi-factor authentication request to the person. Then that person might approve it, thinking this is all a legitimate process.
At this point, the bad actor now has the credentials, and is logged in as that person.
The human might be presented with an screen prompting them for further action, or they may be told the mail was already released and they close it out and go about their day.
Meanwhile, the bad guys are busy putting rules in place to reroute incoming email to a folder so that the human doesn’t see it, and sending email out as the user. Or they could just be laying in wait, harvesting information from the Microsoft user, for days, weeks, months.
Don’t click on random links. Always examine them.
Suspect EVERYTHING.
If your small or medium business needs assistance in the Greenville, Spartanburg, Simpsonville, or Anderson area of the Upstate, let us know. We would be happy to discuss what we can do for you from a computer, server and network sales, service and support perspective!
864-990-4748 x201 or use our contact form.

 The deadline for updating your old Microsoft Windows 10 computers to Windows 11 has come and gone, but it’s likely you don’t feel any different today than you did October 14th – that may change for you, sooner than later.
The deadline for updating your old Microsoft Windows 10 computers to Windows 11 has come and gone, but it’s likely you don’t feel any different today than you did October 14th – that may change for you, sooner than later.